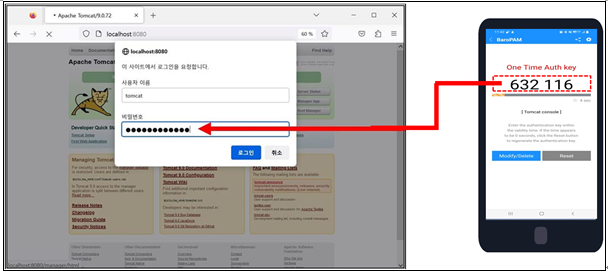
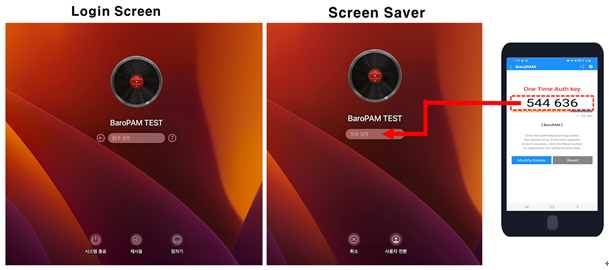
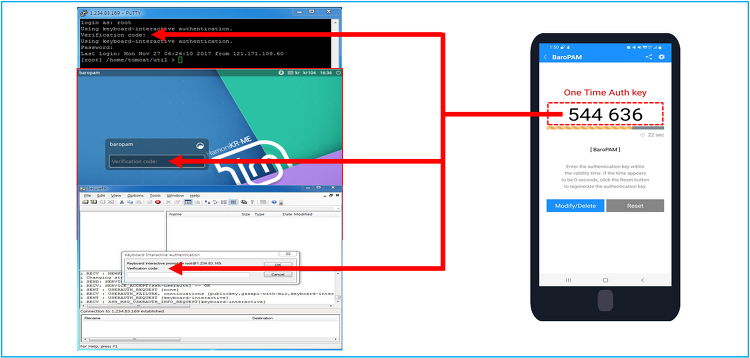
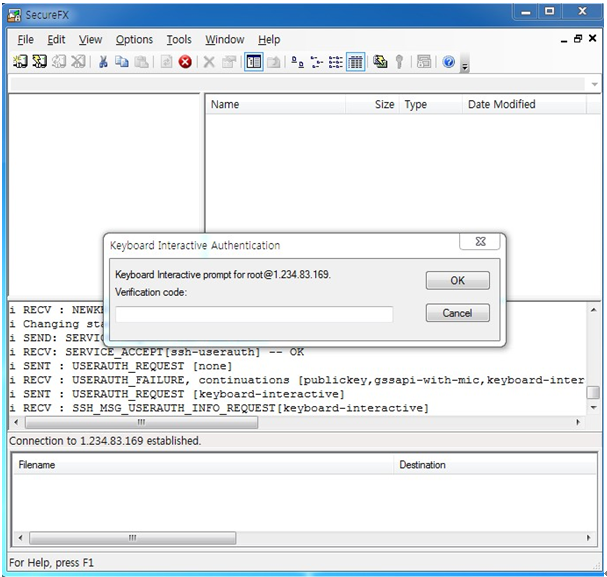
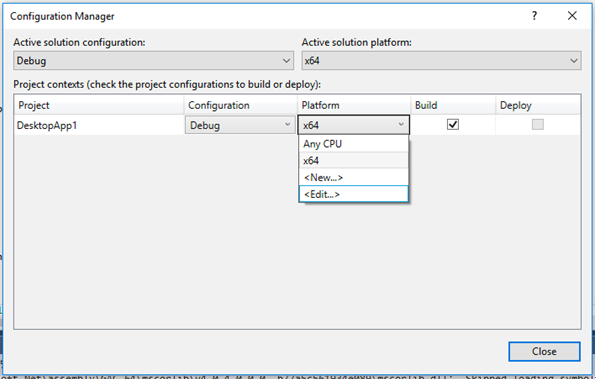
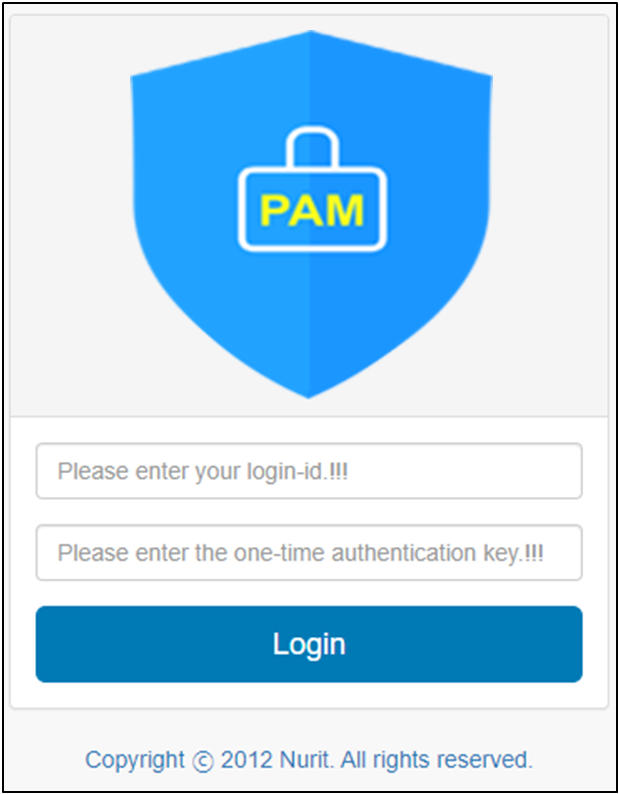
Installation guide for BaroPAM solution for multi-layer authentication to enhance the security of information assets(Tomcat console) Index 1. BaroPAM integration 1.1 Introduction 1.2 Install the BaroPAM module 1.3 BaroPAM configuration 1.4 Install BaroPAM app and set information 2. BaroPAM application 2.1 BaroPAM application process 2.2 BaroPAM application screen 2.3 Login to Tomcat manager cons..